Cloud-Native Security: Protecting Distributed Systems in 2026
As enterprises increasingly migrate workloads to the cloud, traditional security approaches are proving insufficient. The rise of cloud-native architectures—microservices, serverless computing, containerization, and multi-cloud deployments—has created complex, dynamic environments that demand a new approach to security. In 2026, cloud-native security is no longer optional; it’s a critical foundation for protecting distributed systems in an increasingly…
Building an AI-Driven, Post-Quantum Security Strategy
Organizations that want to thrive in a post-quantum, AI-driven world must take a holistic approach: Assess quantum exposure: Identify systems, data, and communications at risk from future quantum attacks. Adopt AI-powered monitoring: Use AI to detect anomalies, predict vulnerabilities, and automate patching and threat response. Integrate post-quantum encryption: Begin implementing PQC where high-risk or long-lived…
Emerging Trends in Artificial Intelligence
Artificial Intelligence (AI) continues to evolve Artificial Intelligence (AI) continues to evolve at an unprecedented pace, impacting diverse sectors and creating dynamic advancements in machine learning algorithms, natural language processing (NLP), and more. Recent breakthroughs in machine learning have led to more accurate prediction models, improved image recognition, and robust decision-making processes. A notable development…
AWS and HUMAIN announce a more than $5B investment to accelerate AI adoption in Saudi Arabia and globally
Amazon Web Services (AWS) and HUMAIN, Saudi Arabia’s newly created company responsible for driving AI innovation across the Kingdom and globally, today announced plans to invest $5 billion-plus in a strategic partnership to build a groundbreaking “AI Zone” in the Kingdom. This first-of-a-kind AI Zone will bring together multiple innovative capabilities, including dedicated AWS AI…
Post-Quantum Cryptography: The Next Frontier
o prepare for quantum threats, enterprises are turning to post-quantum cryptography (PQC). PQC algorithms are designed to resist attacks from both classical and quantum computers. Key initiatives include: Hybrid encryption models: Combining classical and post-quantum algorithms to protect data during the transition period Quantum key distribution (QKD): Using the principles of quantum mechanics to securely…
Intel Unveils Next-Generation 11th-Gen Core H-Series Processors, Revolutionizing Gaming Laptops
Intel, a leading technology company, has made an exciting announcement that is set to transform the gaming laptop market. The company has introduced its highly anticipated 11th Gen Core H-series processors, specifically designed to elevate the gaming experience on laptops. With advanced performance capabilities and cutting-edge features, these processors promise to deliver a new level…
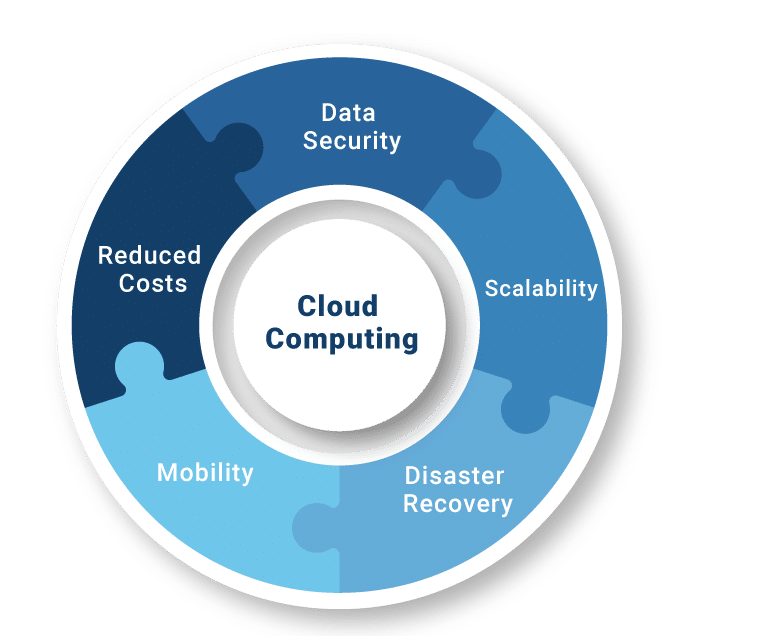
Cloud Computing: Benefits and Challenges
Cloud computing has emerged as a transformative technology, revolutionizing the way businesses store, process, and access data and applications. With its ability to provide scalable and on-demand computing resources over the internet, cloud computing offers numerous benefits to organizations of all sizes. However, like any technological advancement, it also presents its own set of challenges. In this blog, we will explore the benefits and challenges of cloud computing, shedding light on why it has become an integral part of modern IT infrastructure.
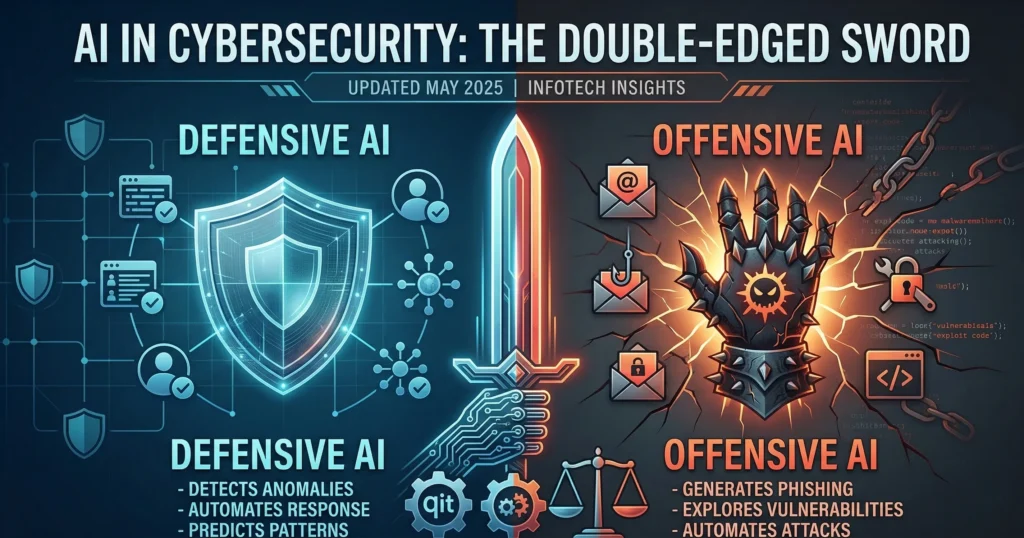
AI in Cybersecurity: Double-Edged Sword
Artificial intelligence is already reshaping cybersecurity in two key ways: Defensive AI: Detects anomalies in network traffic, endpoints, and user behavior Automates threat hunting and incident response Predicts attack patterns before they occur Offensive AI: Generates highly targeted phishing attacks Explores vulnerabilities at scale Automates sophisticated attack campaigns In a post-quantum era, AI’s role will…
The Gartner Top Cybersecurity Predictions 2025-2026
11 July 2025 Join us on July 11, 2023, at 8:30 p.m. IST for a one-hour complimentary cybersecurity webinar that will explore the impact of the pandemic and the rapid acceleration of digital initiatives on organizations. As security and risk management leaders, it is crucial to effectively control and manage disruptions to businesses. To navigate…
AI-Powered Email and Productivity Tools: How AI is Transforming Workflows
In 2026, artificial intelligence is no longer just an enhancement for office tools—it is reshaping the way we work. From intelligent email summaries to AI-driven task management, enterprises are adopting AI-powered productivity solutions to save time, reduce cognitive load, and improve decision-making. One of the most notable examples is Google’s AI Inbox for Gmail, which…
The Future of the Infotech Industry in 2024
Introduction The infotech industry continues to evolve rapidly, and 2024 promises to be a landmark year. Developments in technology are expected to reshape the landscape, presenting both opportunities and challenges. This blog post delves into key trends that will define the infotech sector in the coming year. Emerging Technologies Innovation remains at the heart of…
IT Companies Adapt to GenAI Opportunities Amid Market Slowdown
In the face of a muted market environment, information technology companies are adapting their strategies and shifting the scope of their deals, driven largely by the rising adoption of Generative Artificial Intelligence (GenAI). This emerging technology is reshaping the IT services landscape, presenting both challenges and opportunities for industry players. Shifting Deal Dynamics: As businesses…