Cybersecurity
Microsoft Patches 83 Vulnerabilities
Microsoft on Tuesday announced patches for 83 vulnerabilities affecting its products. While none of the bugs have been flagged as…
This Wing FTP Server flaw is being actively exploited in attacks – CISA says mitigate now
The US Cybersecurity and Infrastructure Security Agency (CISA) has added a new bug to its Known Exploited Vulnerabilities (KEV) catalog,…
Hundreds of Millions of iPhones Can Be Hacked With a New Tool Found in the Wild
A powerful iPhone-hacking technique known as DarkSword has been discovered in use by Russian hackers. It can take over devices…
Top 5 Cybersecurity Companies Leading the Industry in 2026
Cybersecurity is no longer just an IT function—it’s a business survival strategy. With rising ransomware attacks, AI-driven threats, and nation-state…
The Growing Impact of Global Wars on the IT Sector in 2026
Geopolitical tensions and military conflicts increasingly influence the global technology landscape. Wars today are no longer fought only with weapons…
Cybersecurity in the Modern Enterprise: Threats, Prevention, and Compliance
In 2026, cybersecurity is no longer just an IT concern—it’s a core business priority. Modern enterprises face increasingly sophisticated cyber…
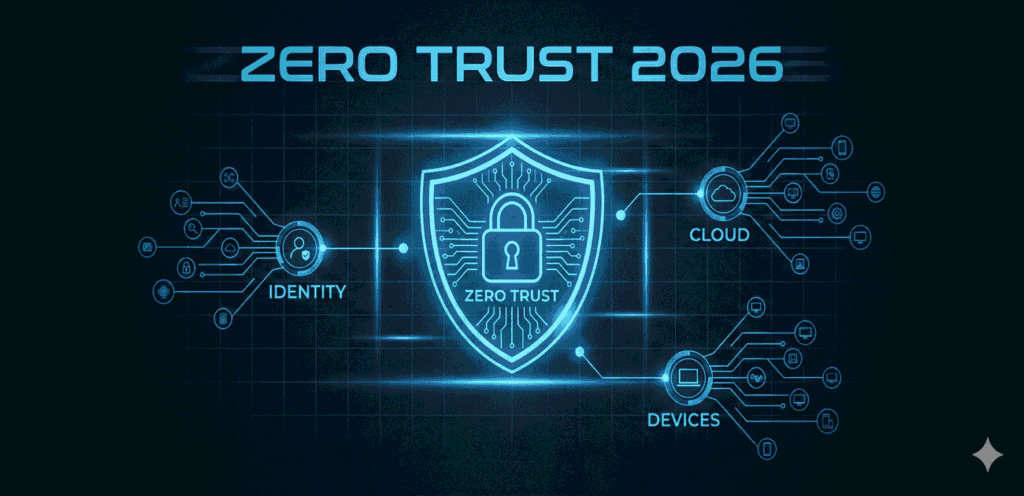
Zero-Trust & Identity-First Cybersecurity in 2026
he cybersecurity perimeter is officially gone. In 2026, enterprises no longer operate within clearly defined networks, and users no longer…
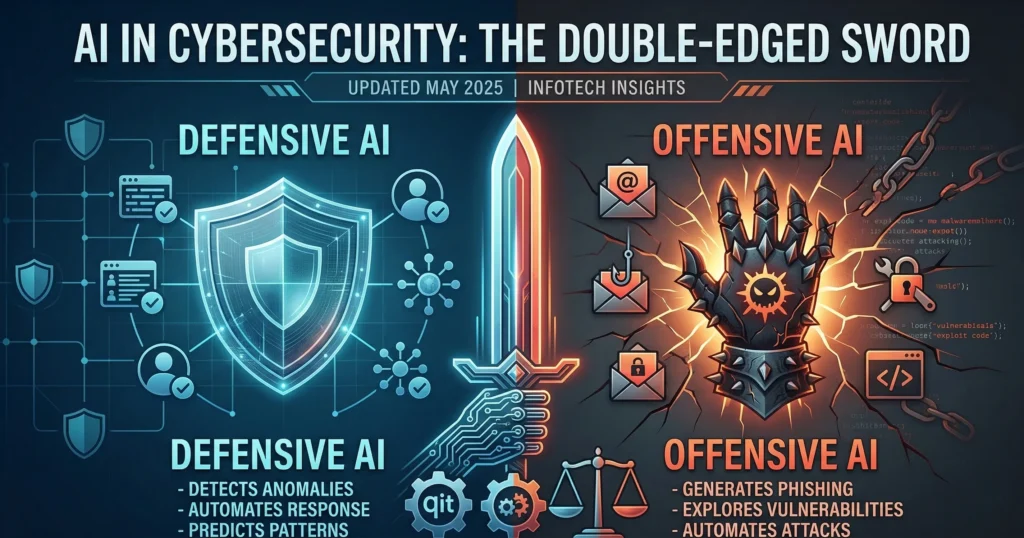
AI in Cybersecurity: Double-Edged Sword
Artificial intelligence is already reshaping cybersecurity in two key ways: Defensive AI: Detects anomalies in network traffic, endpoints, and user…
The Gartner Top Cybersecurity Predictions 2025-2026
11 July 2025 Join us on July 11, 2023, at 8:30 p.m. IST for a one-hour complimentary cybersecurity webinar that…
The Story of Cybersecurity
In this captivating video, we delve into the fascinating story of cybersecurity. From the early days of computer hacking to…